CSE416 Software Engineering course project. Fantasy baseball draft recommendation service. Designed and evolved the cloud infrastructure from a minimal dev setup to a production-grade GKE environment with GitOps CI/CD.
Architecture Evolution
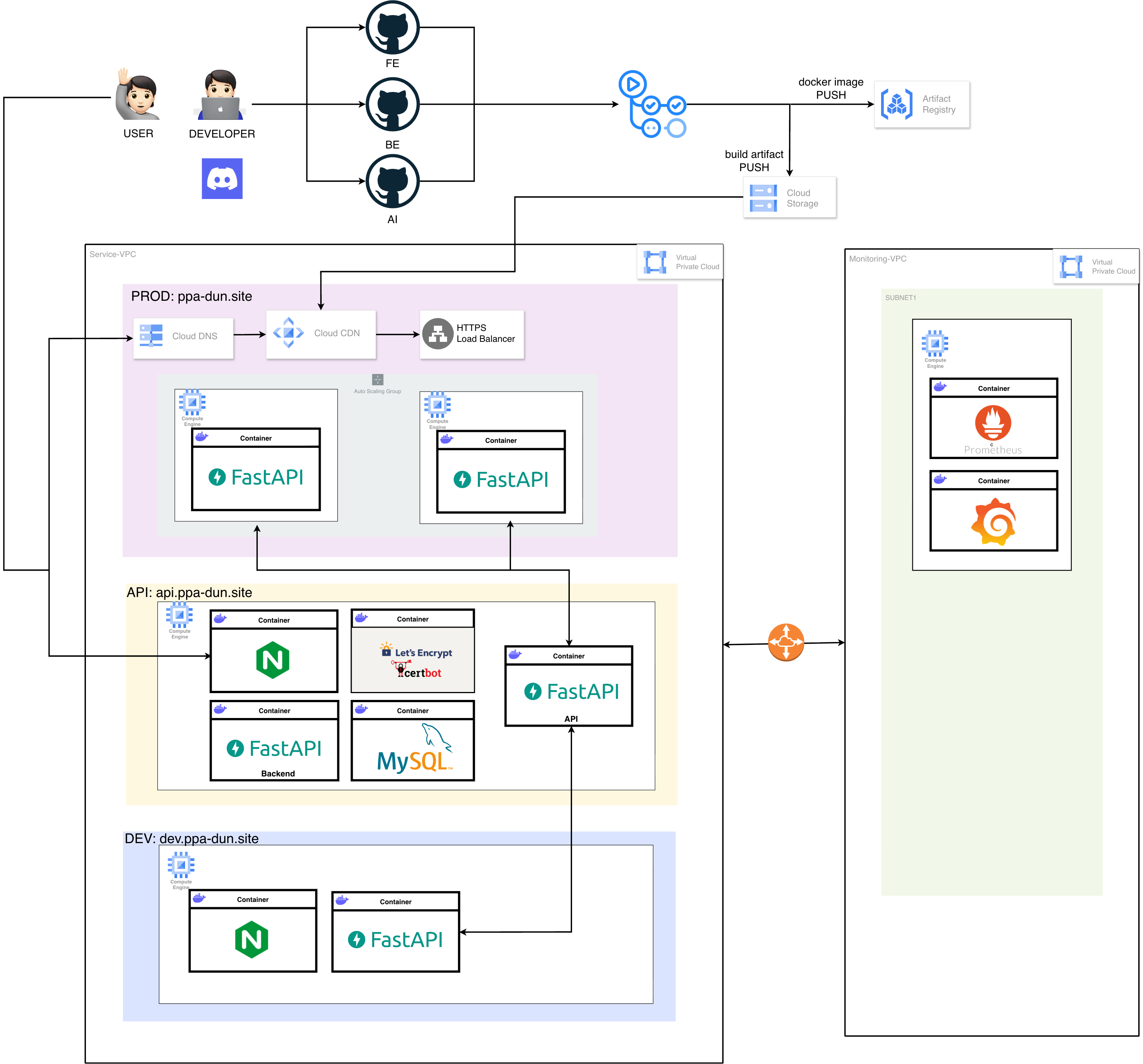
Infrastructure Design
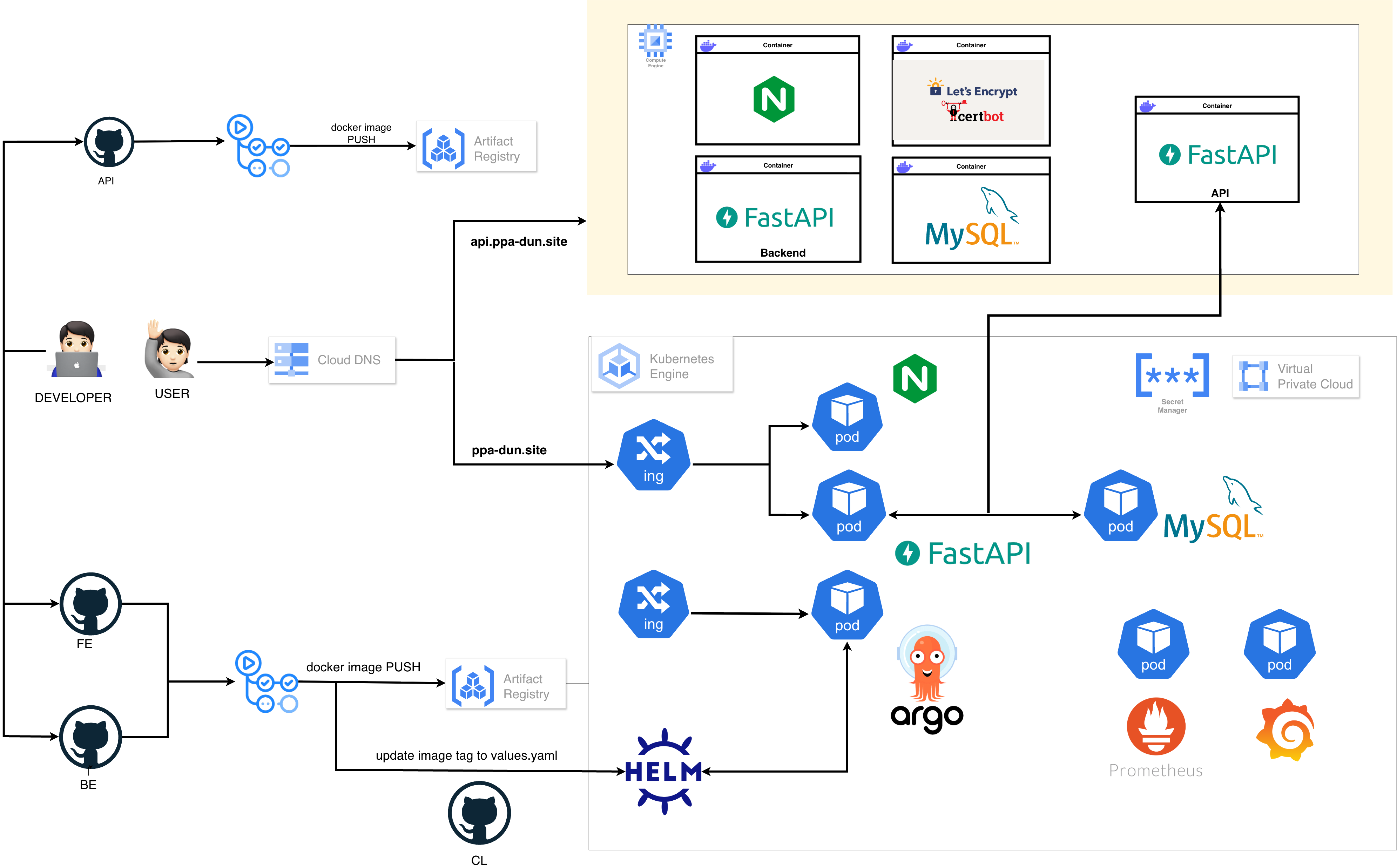
Designed the infrastructure with 2 VPCs connected via VPC Peering — separating application services from monitoring to isolate observability traffic.
System VPC
- DEV subnet
10.10.0.0/16→dev.ppa-dun.site
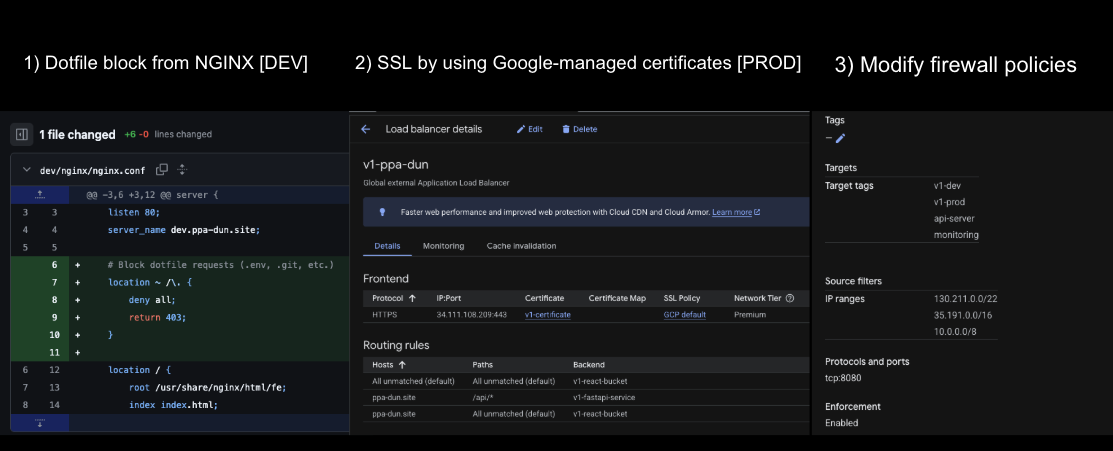
Minimal MVP setup. Single VM with Nginx + Docker (FastAPI + MySQL). No HTTPS, no CDN, HTTP only. Fast iteration for feature development. - PROD subnet
10.20.0.0/16→ppa-dun.site
Production environment with Cloud CDN for frontend caching, Google-managed HTTPS certificate, Global Load Balancer with URL-based routing, and auto-scaling up to 2 instances. - API subnet
10.30.0.0/16→api.ppa-dun.site
Shared API server with Nginx + Let's Encrypt SSL + FastAPI + MySQL. Serves both frontend and external API consumers.
Monitoring VPC
- Monitoring subnet
10.40.0.0/16
Isolated VPC for Prometheus + Grafana. Connected to System VPC via VPC Peering for scraping application metrics without exposing monitoring endpoints.
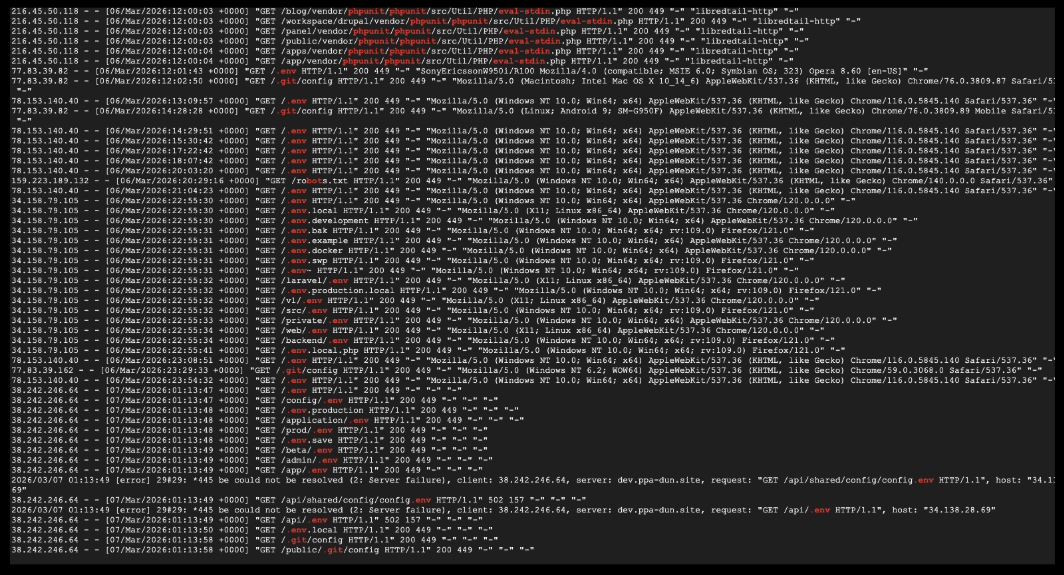
Troubleshooting
Infrastructure Setup
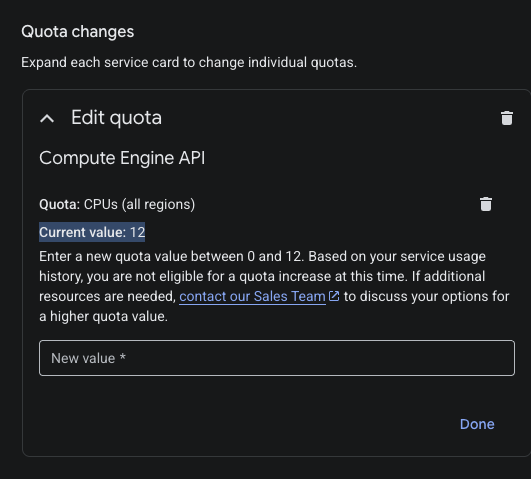
Created a new GCP project (v2-ppa-dun) to isolate GKE resources from the v1 project and work around the CPU quota constraint. All infrastructure provisioned via Terraform:
| Terraform File | Resources |
|---|---|
| vpc.tf | New VPC + Subnet (10.50.0.0/16) |
| gke.tf | GKE Autopilot cluster (nodes managed by GKE) |
| secrets.tf | GCP Secret Manager secrets (DB credentials, API keys) |
| workload-identity.tf | GCP SA ↔ K8s SA binding for Secret Manager access |
Application deployment managed via Helm chart + ArgoCD GitOps:
- Helm — Templated K8s manifests for frontend (Nginx), backend (FastAPI), Ingress, SSL, and secrets
- ArgoCD — Watches the Helm chart repo. Git push triggers automatic sync and pod redeployment
- External Secrets Operator — Syncs GCP Secret Manager → K8s Secrets via Workload Identity (no credentials in Git)
- GKE Ingress — Global LB with Google-managed SSL certificate for
ppa-dun.site